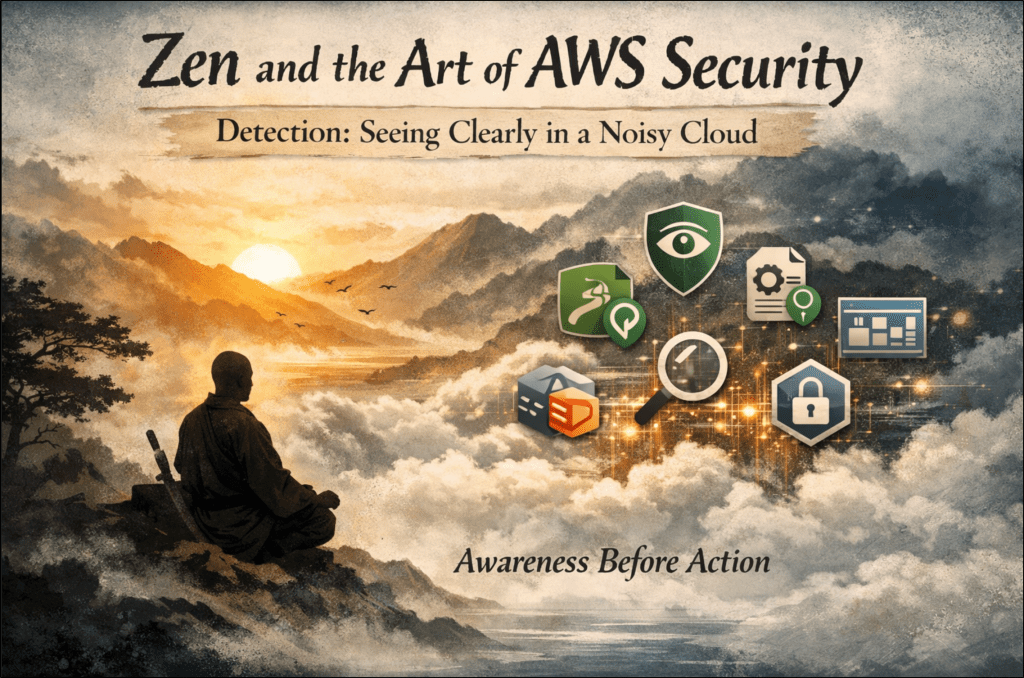
Domain 1: Detection – Hearing and Seeing Clearly in the Cloud
There’s a saying in martial arts that applies perfectly to cloud security: “Awareness prevents more fights than strength.”
Most people think security begins with blocking, encryption, denial, and restriction. But AWS and attackers know differently. The real starting point is detection. You can’t defend what you can’t see, and you can’t respond to what you never noticed.
This is why Detection is Domain 1 on the AWS Security Specialty exam. Not because it’s the most technical topic, but because every other domain depends on it.
Identity, data protection, incident response, and infrastructure security all collapse the moment visibility disappears. In the cloud, as in combat, clarity is the highest security control.
1. AWS’s Philosophy of Detection
AWS designs detection around a core assumption: You cannot rely on perimeter security in a distributed, API-driven system.
Instead, AWS builds around three principles:
- Every meaningful action must generate a log. Not optional. Not “best effort.” Mandatory.
- Threat detection must be continuous and automated. The cloud moves faster than human reaction time.
- Context matters more than isolated events. A single API call means very little.
A pattern of calls can mean everything.
The exam tests whether you understand this mindset—not whether you memorized service names.
Once you internalize the philosophy, the questions stop feeling tricky. They start feeling predictable.
2. Core Detection Services – What They Do & Why AWS Tests Them
Below is the high-value, exam-relevant, no-fluff breakdown of AWS detection services, explained the way AWS expects you to reason about them.
AWS CloudTrail – The Source of Truth, Telling You Who Did What
CloudTrail records:
- Who made the request
- When it occurred
- From where
- Against which service
- And the result
If a question mentions API activity, auditing, investigation, or root cause, the correct answer almost always includes:
- CloudTrail enabled
- centralized log storage (S3)
- encryption (SSE-KMS)
- optional CloudTrail Insights for anomalies
Exam mental model: If you’re reconstructing events, start with CloudTrail.
Case in point: In 2019, Capital One suffered a major data breach in their AWS environment. Investigators traced the attack using CloudTrail logs, which revealed how a misconfigured firewall and stolen credentials allowed unauthorized access. This incident underscores why robust detection and logging aren’t just about passing the exam; they’re essential for real-world defense and forensic investigation.
CloudTrail isn’t just a checkbox when breaches happen; it’s often the first and last line of forensic defense.
AWS Config – The Historian Letting You Know What Changed?
Config tracks:
- configuration changes
- compliance drift
- deviations from approved baselines
If the question mentions misconfiguration, continuous compliance, governance, or drift, the answer is:
- AWS Config
- Config Rules
- Aggregators (for multi-account visibility)
Exam pattern callout: If a question mentions misconfiguration, compliance drift, or unexpected changes, AWS Config is usually the answer.
Exam mental model: If something shouldn’t have changed, but did, Config already knows. Config is your early warning system for risky changes, catching drift before it becomes a compromise.
Amazon GuardDuty – The Sentinel Letting You Know “If Anything Is Behaving Abnormally
GuardDuty detects:
- anomalous IAM behavior
- malicious API usage
- compromised EC2 instances
- suspicious network activity
- data exfiltration indicators
It is:
- agentless
- continuously running
- driven by AWS threat intelligence
If the question mentions anomaly, unexpected behavior, suspicious activity, or threat intel, the answer is almost always: GuardDuty
Exam pattern callout: If the question mentions anomaly detection, threat intelligence, or suspicious behavior, GuardDuty is the right choice.
Exam mental model: When AWS wants you to detect weirdness, choose GuardDuty.
GuardDuty’s findings are your heads-up display—if it’s alerting, pay attention before a minor issue becomes a major breach.
Amazon Detective – The Investigator, Tells You Why Things Happened
Detective correlates:
- CloudTrail
- GuardDuty
- VPC Flow Logs
…into a graph-based model showing relationships between events.
If the question mentions:
- root cause analysis
- investigation
- relationships between actions
- tracing an incident timeline
The answer likely includes: Detective
Exam pattern callout: For root cause analysis, investigation, or connecting actions across services, Detective is the answer.
Exam mental model: GuardDuty alerts you. Detective explains it.
Detective is your investigation toolkit, connecting the dots when the story isn’t obvious from a single log or alert.
AWS IAM Access Analyzer – The Boundary Checker
Access Analyzer identifies:
- unintended public access
- unintended cross-account access
- overly permissive resource policies
If the question involves:
- S3 exposure
- IAM trust policies
- KMS, ECR, or EKS access
- cross-account risk
Answer: Access Analyzer
Exam pattern callout: If the question involves S3 exposure, overly permissive policies, or cross-account access, think Access Analyzer.
Exam mental model: Resource policy exposure = Access Analyzer.
Access Analyzer is your reality check, proactively surfacing risky permissions before the wrong person finds them.
AWS Security Hub – The Fusion Center
Security Hub:
- aggregates findings
- normalizes severity
- provides centralized visibility
It pulls from:
- GuardDuty
- Inspector
- IAM Access Analyzer
- Macie
- custom sources
If the question says “centralized findings”, “single pane of glass”, or “consolidated security view”, the answer is: Security Hub
Exam pattern callout: If the question asks about centralized findings, “single pane of glass,” or consolidated security data, Security Hub is the answer.
Exam mental model: Security Hub does not detect. It collects.
Security Hub is your security operations dashboard where all findings converge for centralized action.
3. Detection Exam Patterns – These Score You Points Quickly
AWS exam writers love pattern recognition.
Memorize these:
- “Who did what?” → CloudTrail
- “Unexpected behavior” → GuardDuty
- “Investigate a finding” → Detective
- “Cross-account exposure” → Access Analyzer
- “Continuous compliance” → Config
- “Centralized visibility” → Security Hub
These patterns alone solve a large percentage of Domain 1 questions.
4. Detection Is the Art of Paying Attention
Detection is not about tools. Tools amplify awareness; they don’t replace it.
Attackers understand this. That’s why social engineering works: it hijacks attention.
Propaganda uses the same mechanism:
- control attention
- shape perception
- influence behavior
Detection in AWS is the defensive inversion of that logic:
Expand awareness → clarify perception → prevent escalation.
Detection isn’t about catching bad actors. It’s about not being surprised.
In martial arts, that’s everything. If you anticipate the strike, the strike no longer matters.
5. The Martial Parallel: Awareness Before Technique
Technique without awareness is empty.
You can block perfectly, but only if you can see or feel the strike coming.
You can counter cleanly, but only if you read the motion correctly.
In AWS:
- CloudTrail is your eyes.
- Config is your memory.
- GuardDuty is your instincts.
- Detective is your reasoning.
- Access Analyzer is your boundary sense.
- Security Hub is your situational awareness.
Without awareness, technique becomes panic. With awareness, technique becomes effortless.
6. Closing: The Quiet Strength of Clear Insight
Detection is the least glamorous domain.
No firewalls to tune.
No keys to rotate.
No dashboards that make you feel heroic.
And yet, everything depends on it.
A well-architected detection strategy:
- eliminates blind spots
- accelerates incident response
- surfaces misconfigurations early
- strengthens identity boundaries
- anchors governance
On the exam, clarity is the deciding factor.
Domain 1 rewards candidates who pause, breathe, and reason, rather than react.
Security without pessimism begins here:
See clearly.
Think clearly.
Move deliberately.
Obviously, the detection process isn’t paranoia. It’s awareness of what’s going on in your environment. And awareness is where security and mastery begin. Detection isn’t just an exam topic; it’s the first line of defense in every real cloud breach.
Verification & Citations Framework (Leave No Doubt)
Authoritative AWS Sources Used for The AWS Security Specialty (SCS-C03)
Domain 1 Detection:
- AWS CloudTrail Documentation
- Amazon GuardDuty Documentation
- AWS Config Documentation
- Amazon Detective Documentation
- IAM Access Analyzer Documentation
- AWS Security Hub Documentation
Verification Checklist:
- Services mapped to AWS exam guide Domain 1
- Descriptions align with AWS documentation language
- Mental models reflect AWS exam question patterns
- No unsupported claims or third-party assumptions
Change Awareness Note:
AWS services evolve. Always confirm current feature behavior against official AWS documentation prior to exam or implementation.