When Experience Becomes the Blind Spot

You’ve been in tech long enough to spot the obvious scams. They have bad grammar, sketchy links, and the “urgent” password resets that scream, “It’s a trap.”
Modern phishing is designed for experienced professionals, people just like you.
The senior engineer who knows better.
The manager who moves fast.
The admin is juggling too many tabs.
Phishing 2.0 targets the confident, not the naive.
Because overconfidence, that quiet, “I’d never fall for that,” is exactly what gets exploited.
How Phishing Evolved While We Were Busy
Old-school phishing was obvious: typos, weird logos, fake banks. Now? It’s clean, professional, and personalized.
Attackers scrape LinkedIn, GitHub, and Slack leaks, as well as any other platform where they can learn who you are and how you communicate. Then they build emails that sound right.
“Following up on that architecture review.”
“Can you sign off on the AWS access request?”
No panic. No red flags. Just believable context. Phishing’s power now lies in familiarity, not just deception.
The Psychology And Why Smart People Click Anyway
It’s not ignorance. It’s pattern recognition. Your brain runs on shortcuts. You see what fits your norm and fill in the rest. “This feels familiar, so it’s safe.”
Layer on fatigue, distraction, or context switching, and even the most security-conscious person can click the wrong thing.
Attackers don’t need to outsmart you, they just need to catch you mid-scroll.
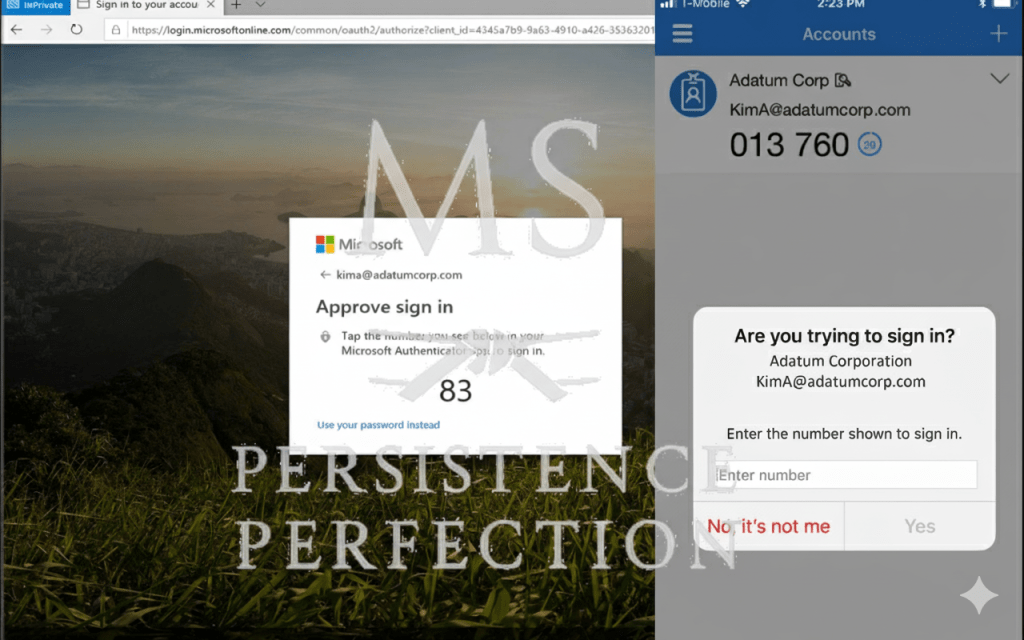
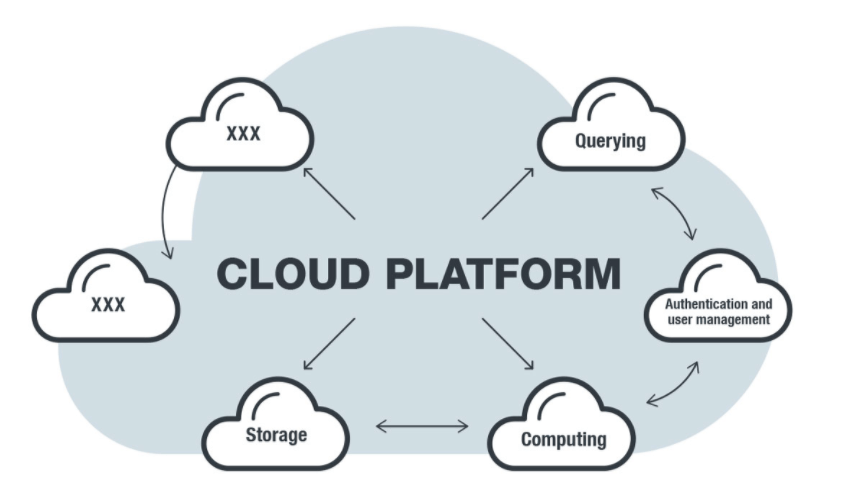
The Real Tricks How Phishers Use Your Own Systems Against You
Phishing 2.0 thrives inside your workflow:
- Cloud notifications: “New file shared with you.”
- Team apps: Slack, Notion, or Asana lookalikes.
- Vendor portals and HR systems: identical clones.
- QR codes: the new “scan to verify” scam.
Attackers don’t mimic strangers anymore; they mimic your routine.
The antidote, and our greatest protection, is patience.
Forget fear. Focus on tempo.
Build a habit of thinking first, then reacting. Believe me, I know it sounds elementary and maybe even silly, but people do it every day. It reminds me of the old saying from the range: “ready, fire, aim” versus “ready, aim, fire.” People are often too quick to react without pausing to think first.
That moment of pause between seeing and clicking is what saves the enterprise. So, always:
- Hover first. Always.
- Verify context: Does it match your current workflow?
- Cross-check by text or chat before responding.
- Trust your instinct; hesitation usually means something’s off.
Security isn’t about paranoia. It’s about building patience as your strongest defense.
Culture Over Blame
Curiosity beats compliance. Blaming users for falling for a phishing attempt isn’t awareness training or good security; it’s just scapegoating. People click because they’re human, not because they don’t care.
If your environment rewards speed over care, mistakes are inevitable. Instead of punishment, build openness to conversation. A strong security culture treats “I think I clicked something bad” as a start, not a sin.
Curiosity beats complacency every time.
Final Thought
Phishing 2.0 isn’t just a tech problem; it’s a problem of pace. Attackers take advantage of our work tempo. The faster we move, the easier it is to miss what matters.

The best security upgrade?
Breathe. Scan well. Challenge every unfamiliar link or request. Pause before you click, verify before you act, and encourage your team to do the same.
That’s not being cynical or pessimistic.
That’s the difference: real security means trained, patient awareness every day.